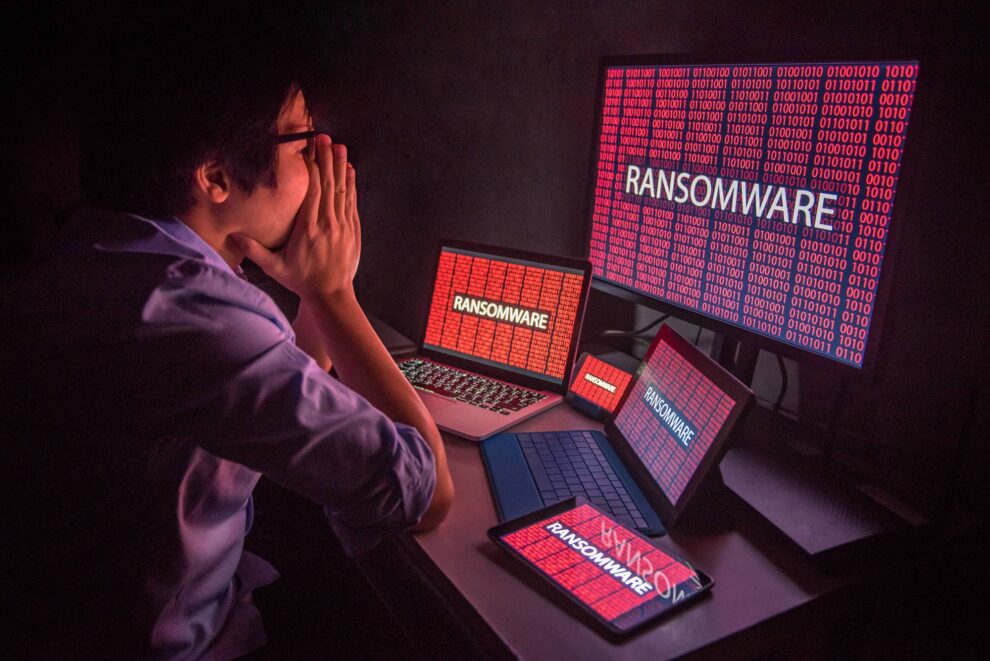
According to a study by IBM, globally, ransomware is decreasing, but in Latin America, it has increased by 3%.
Attempts to hijack email conversations have intensified worldwide; criminals execute ransomware attacks in days rather than months, and the retail and wholesale sectors are the most targeted in Latin America.
IBM Security published its annual X-Force Threat Intelligence Index report, finding that while the percentage of global ransomware incidents decreased slightly (by four percentage points) from 2021 to 2022, it increased somewhat (by three percentage points) in Latin America. Although defenders had more success in detecting and preventing ransomware, attackers have continued to innovate. The report shows that the average time to complete a ransomware attack decreased from two months to less than four days.
According to the 2023 report, the implementation of backdoors, which allow remote access to systems, emerged as the second most common action taken by attackers in the region in the past year. Many of these backdoor cases were related to ransomware attempts, in which defenders detect the backdoors before any ransomware implementation. Partially, the resurgence in backdoor performances is their high market value. X-Force observed that threat actors sell existing backdoor access on the dark web for up to US$10,000 compared to stolen credit card data, which currently sells for less than US$10.
The state of ransomware and cyberattacks in the region
The IBM Security X-Force Threat Intelligence Index monitors trends and patterns of new and existing attacks based on billions of data points from network devices and endpoints, their incident response involvement, and other sources. Here are some key findings from the latest report in Latin America:
- The region is gaining importance for cybercriminals. Although Latin America accounted for 12% of the attacks observed by the X-Force incident response team, the area moved from the fifth to the fourth most targeted region globally.
- Top targeted countries in Latin America in 2022. In all cases responded to by X-Force in Latin America, Brazil accounted for 67%, Colombia for 17% and Mexico for 8%. Peru and Chile accounted for the remaining 8%.
- Retail and wholesale sectors were the most targeted. Incidents in Latin America went against global industry trends. The retail and wholesale sector moved from second place to the most targeted industry in 2022, representing 28% of the cases resolved by X-Force. Finance and insurance were the second most targeted sector, with 24% of the cases, followed by energy and manufacturing, both with 20%.
- Business Email Compromise (BEC) decreased in the region. BEC ranked third in 2022, accounting for 11% of the incidents responded to by X-Force. This attack occurs when a server is accessed to achieve unknown end goals. Attackers primarily used spear-phishing links, malicious attachments and exploitation of valid accounts to gain access.
- Cybercriminals exploit email conversations. Email thread hijacking significantly increased in 2022, with attackers using compromised accounts to respond to ongoing discussions, pretending to be the original participant. X-Force observed a 100% increase in monthly global attempts. Email conversation hijacking accounted for 11% of the attacks in the region.
- Extortion is the preferred method of threat actors. One of the most common impacts of cyberattacks last year in the region was extortion, mainly achieved through ransomware or BEC attacks, reflecting the global trend. Cybercriminals primarily target the most vulnerable sectors, companies and areas using extortion schemes and applying high psychological pressure to force victims to pay.
- Ransomware surpassed other attacks in Latin America, representing 32% of the cases responded to by X-Force. Implementing backdoors was the second most identified action against targets, at 16%, while BEC and email thread hijacking tied for third place at 11% each. Extortion and data theft were the most frequent impacts in the region, accounting for 27% of the cases, followed by financial losses at 20%. Data destruction and leaks tied for third place, each at 13% of the cases.
Some of the global findings from the 2023 report include:
- Phishers ‘give up’ on credit card data. The number of cybercriminals targeting credit card information in phishing kits dropped by 52% in a year, indicating that cyberattackers prioritize personal identification information, such as names, emails and addresses, that may sell at a higher price on the Dark Web or for using in further operations.
- Legacy security vulnerabilities still do the job. The percentage of security exploits related to exposures decreased by 10 points from 2018 to 2022, as the number of vulnerabilities reached another record in 2022. The findings indicate that legacy security vulnerabilities allow older malware infections like WannaCry and Conficker to continue existing and spreading.
- Most impersonated brands include major technology companies. Stolen credentials from these services are valuable for accessing accounts that victims use to manage their online presence. X-Force believes that this shift in the list towards a more diverse range of brands is due to the improved ability to identify the brands that a kit can impersonate, not just the default target.
The report presents globally collected data by IBM to provide relevant information about the global threat landscape and inform the security community about the most pertinent threats to their organizations.
Source : IntelligentCIO